Attachments can be inspected by creating Exchange Transport rules, We had this option earlier however not really worked as expected, Now it is working as expected. This article applies for Exchange & Office365.
Below source : Technet
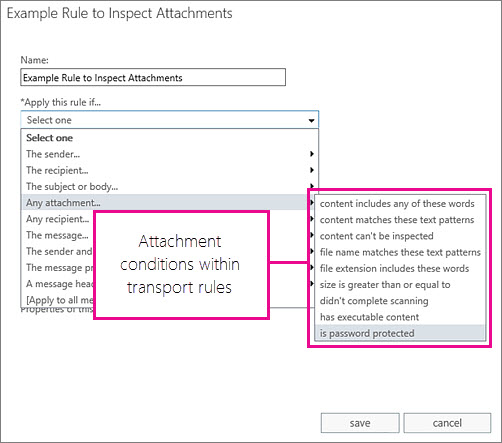
Conditions can be applied for transport rules:
| Condition name in EAC | Condition name in the Shell | Description |
|---|---|---|
| Any attachment file name matches these text patterns | AttachmentNameMatchesPatterns |
This condition matches messages with supported file type attachments when those attachments have a name that contains the characters you specify. |
| Any attachment file extension includes these words | AttachmentExtensionMatchesWords |
This condition matches messages with supported file type attachments when the file name extension matches what you specify. |
| Any attachment size is greater than or equal to | AttachmentSizeOver |
This condition matches messages with supported file type attachments when those attachments are larger than the size you specify. |
| Any attachment didn’t complete scanning | AttachmentProcessingLimitExceeded |
This condition matches messages when an attachment is not inspected by the transport rules agent. |
| Any attachment has executable content | AttachmentHasExecutableContent |
This condition matches messages that contain executable files as attachments. The supported file types are listed here. |
| Any attachment is password protected | AttachmentIsPasswordProtected |
This condition matches messages with supported file type attachments when those attachments are protected by a password. |
The Exchange Management Shell names for the conditions listed here are parameters that require the TransportRule cmdlet.
The transport agent uses true type detection by inspecting file properties rather than merely the file extensions. This helps to prevent malicious hackers from being able to bypass your rule by renaming a file extension. The following table lists the executable file types supported by these conditions. If a file is found that is not listed here, the AttachmentIsUnsupported condition is triggered.
| Type of file | Native extension |
|---|---|
| Self-extracting archive file created with the WinRAR archiver. | .rar |
| 32-bit Windows executable file with a dynamic link library extension. | .dll |
| Self-extracting executable program file. | .exe |
| Java archive file. | .jar |
| Uninstallation executable file. | .exe |
| Program shortcut file. | .exe |
| Compiled source code file or 3-D object file or sequence file. | .obj |
| 32-bit Windows executable file. | .exe |
| Microsoft Visio XML drawing file. | .vxd |
| OS/2 operating system file. | .os2 |
| 16-bit Windows executable file. | .w16 |
| Disk-operating system file. | .dos |
| European Institute for Computer Antivirus Research standard antivirus test file. | .com |
| Windows program information file. | .pif |
| Windows executable program file. | .exe |
Good One! Can we use this for internal email routing if we are using third party spam filtering like ironport/proofpoint.
Thanks,
yes, you can change the condition to meet the requirement.