In continuation with my previous post, we will be deploying the Enterprise Subordinate Issuing CA in the second forest.
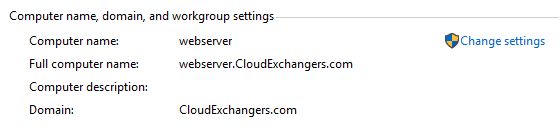
Forest B: CloudExchangers.com
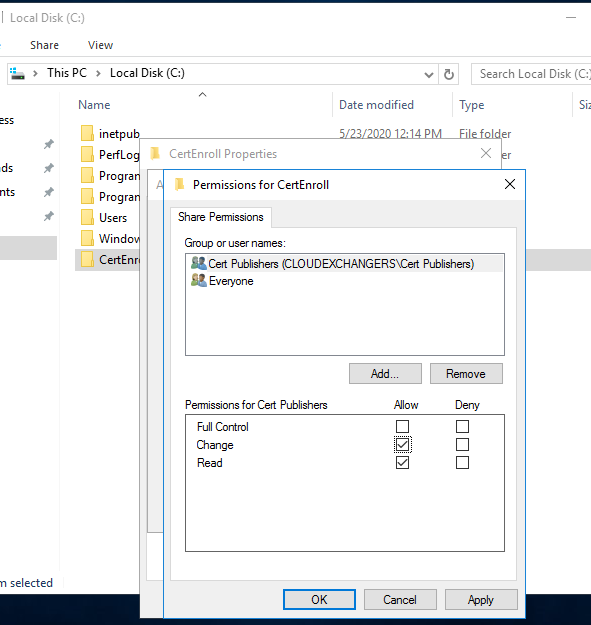
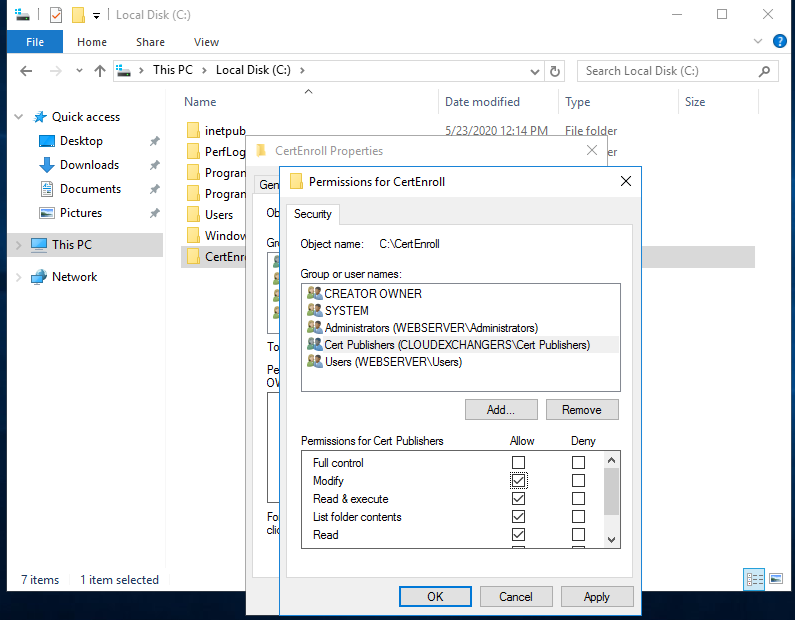
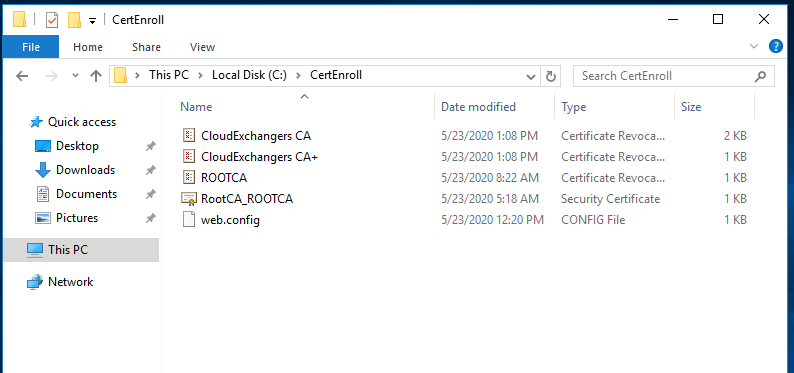
Create a folder “CertEnroll” and provide “cert publishers” change permissions on sharing and “modify” on the security permissions.
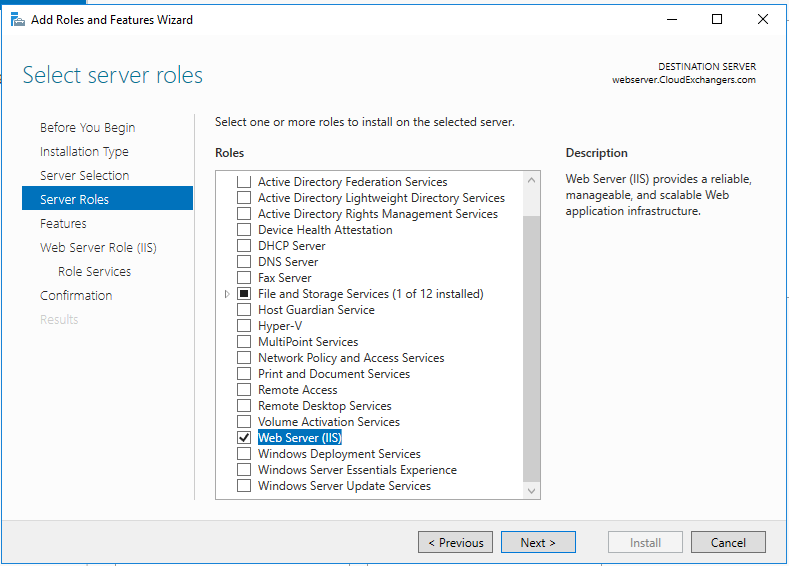
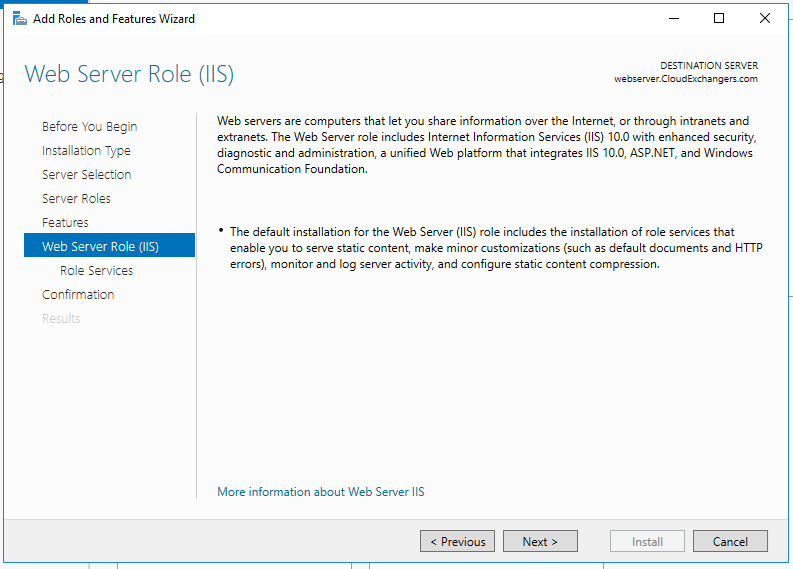
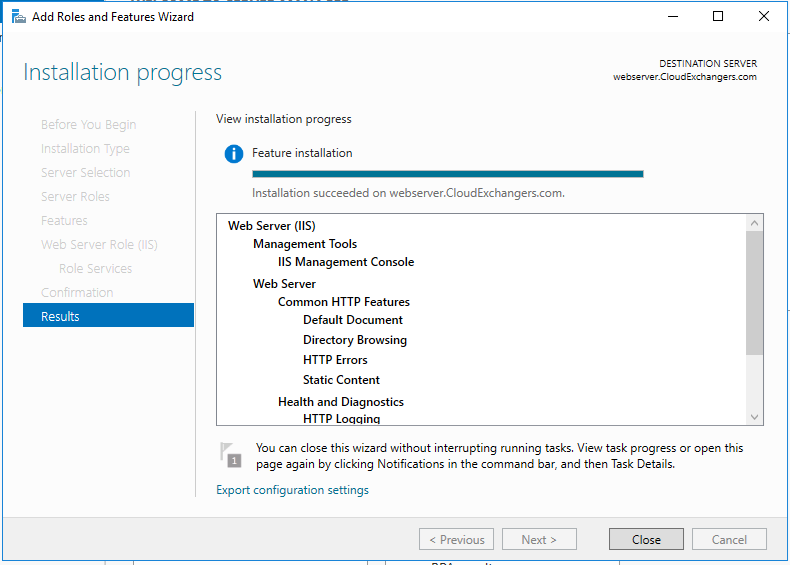
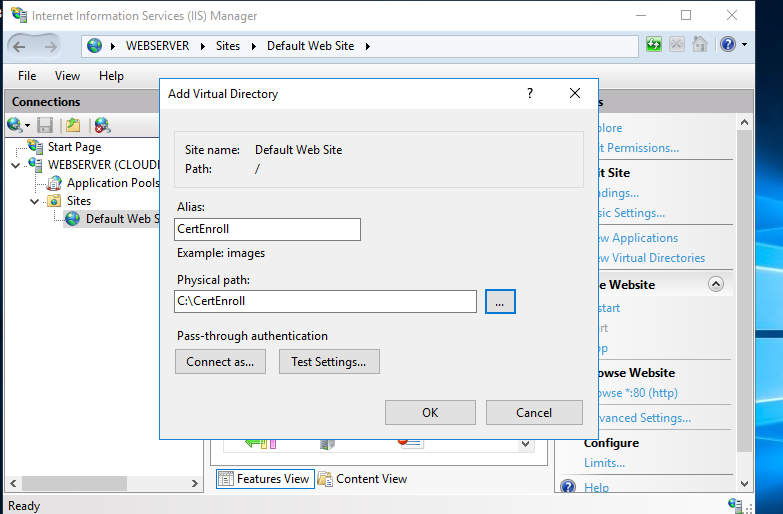
Open the IIS manager, create a new virtual directory and provide the details as below,
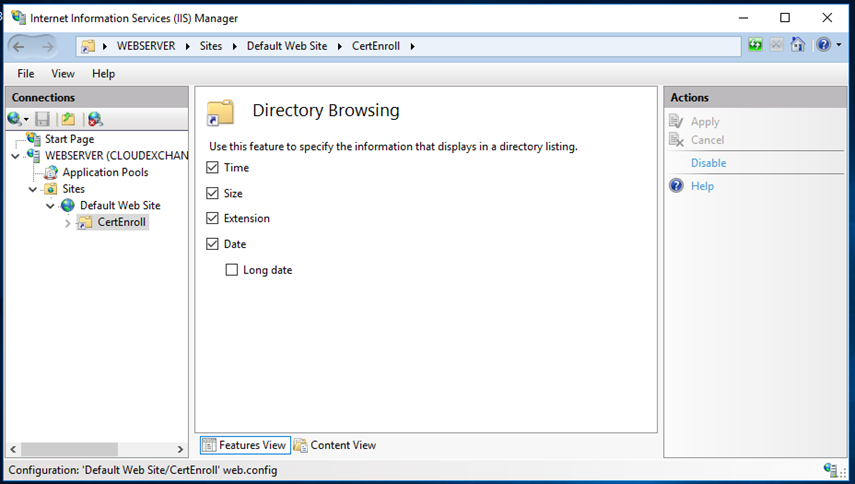
Enable the directory browsing,
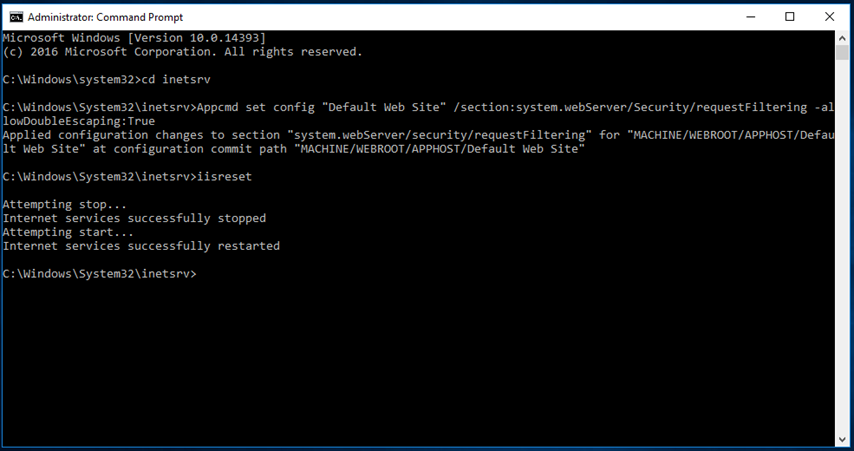
Enable the Double Escaping, this will allow the web server to host Delta CRLs
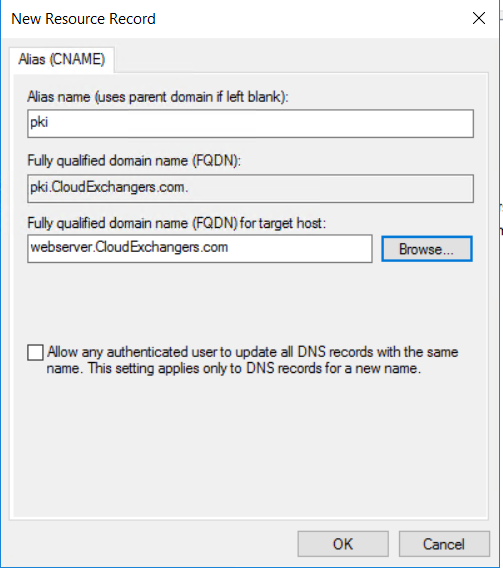
DNS record creation for pki.cloudexchangers.com,
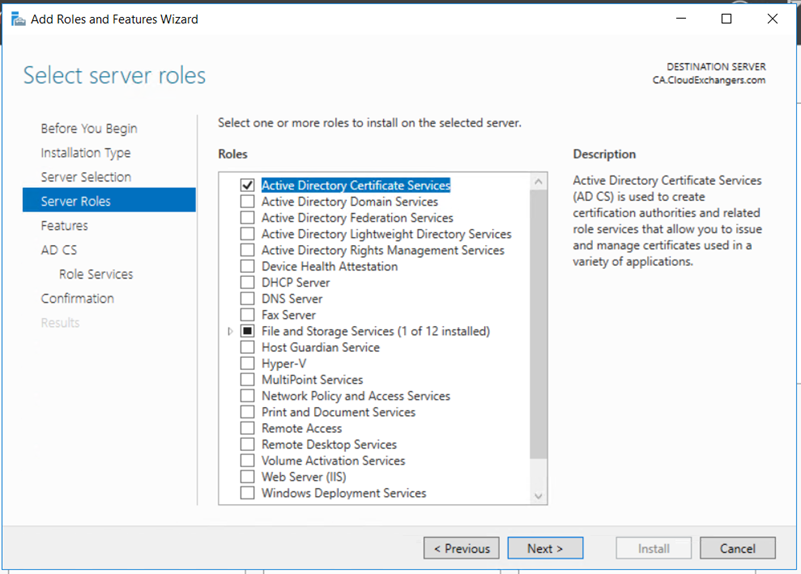
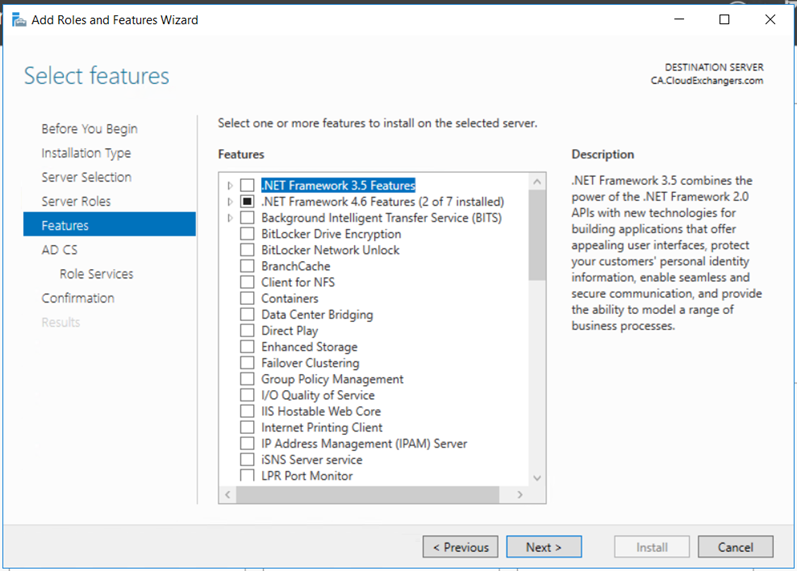
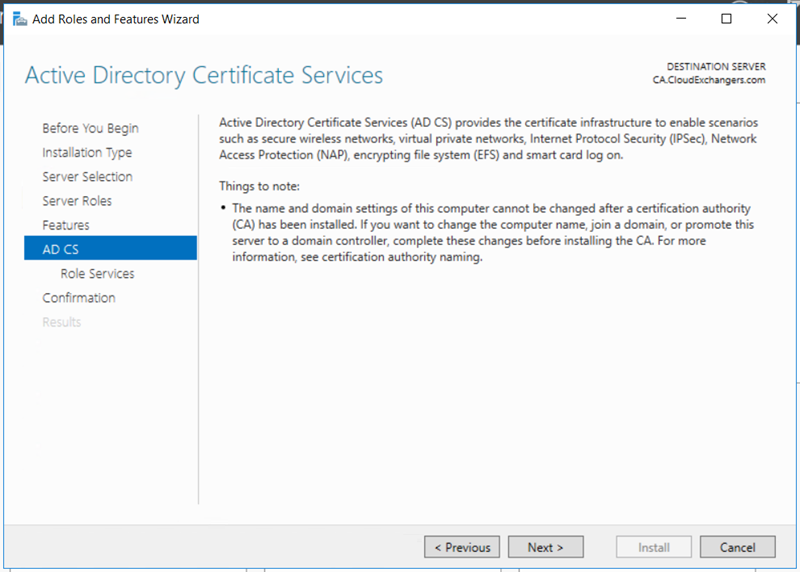
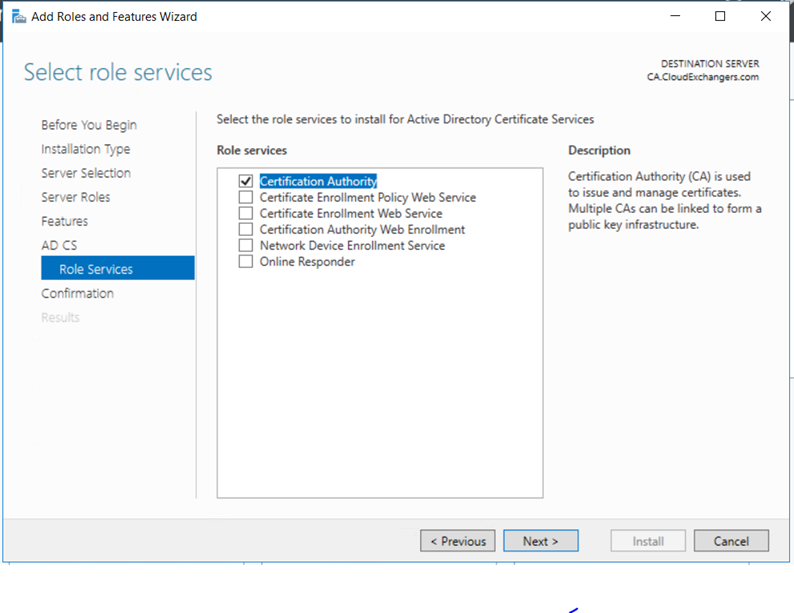
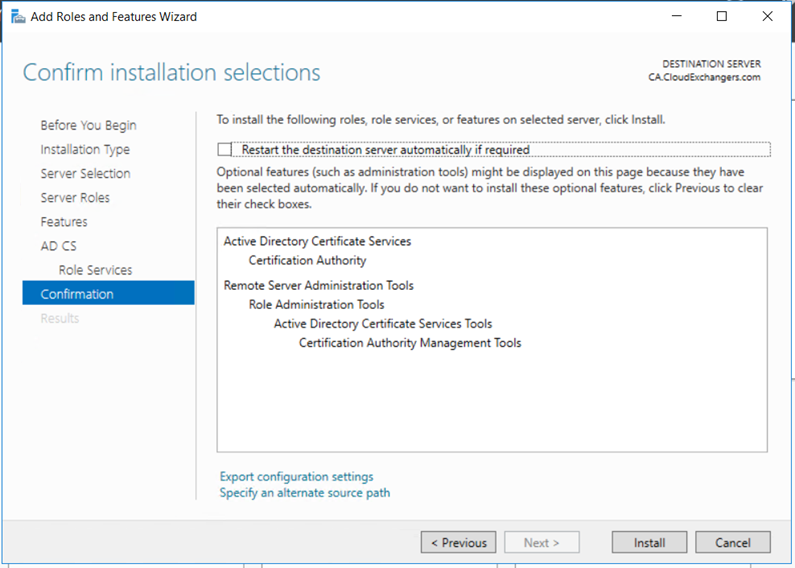
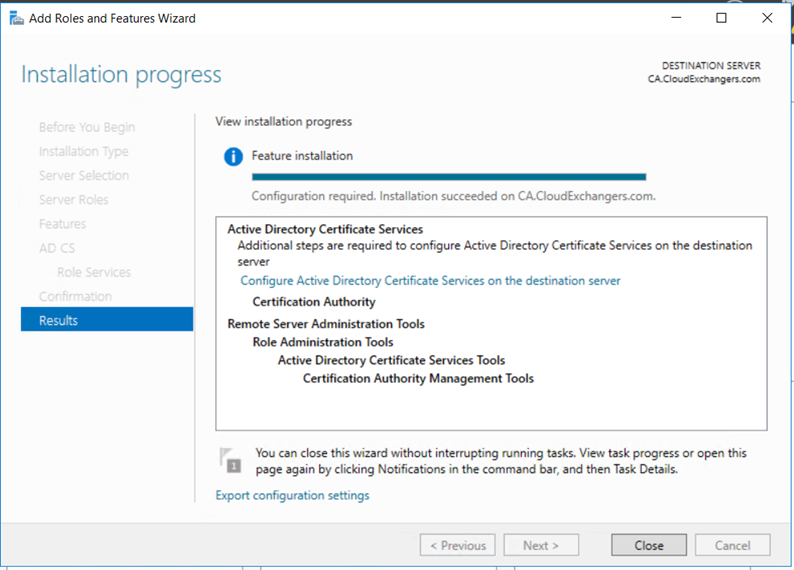
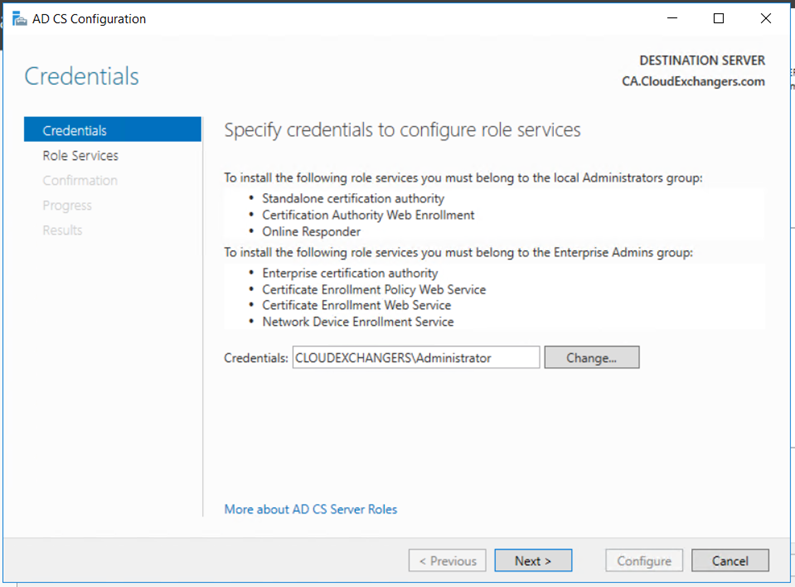
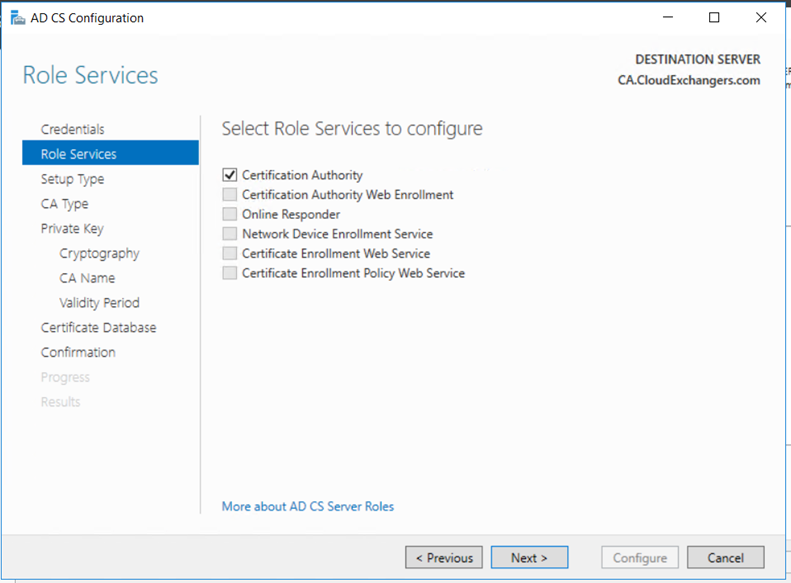
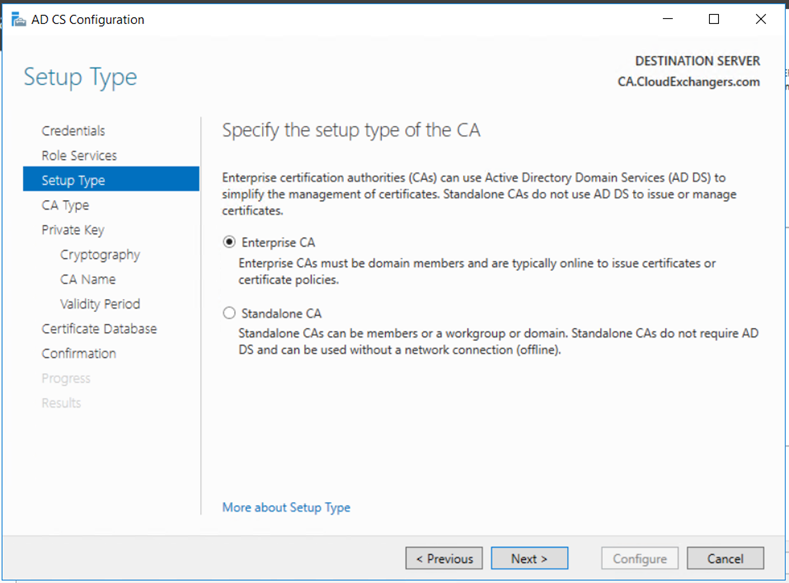
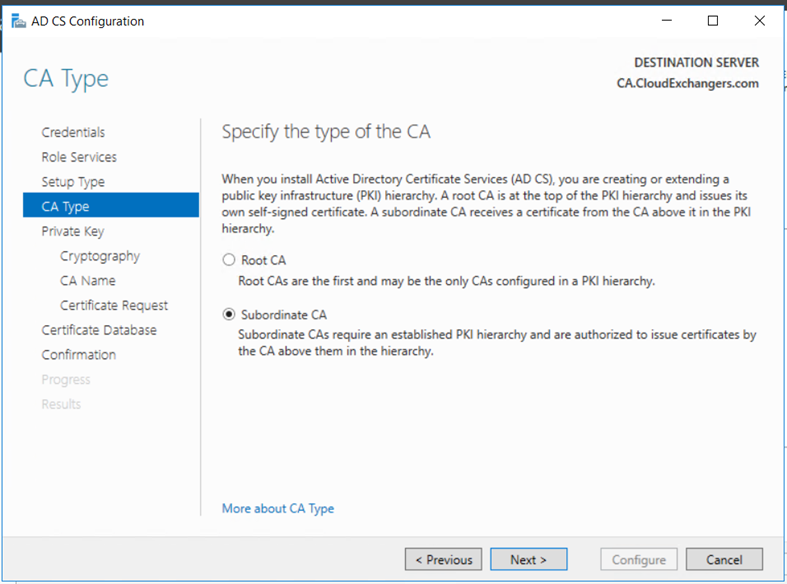
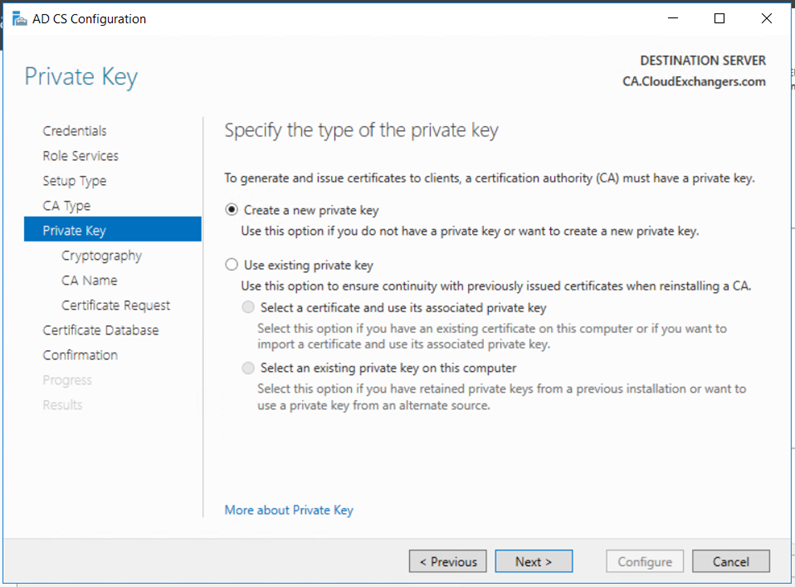
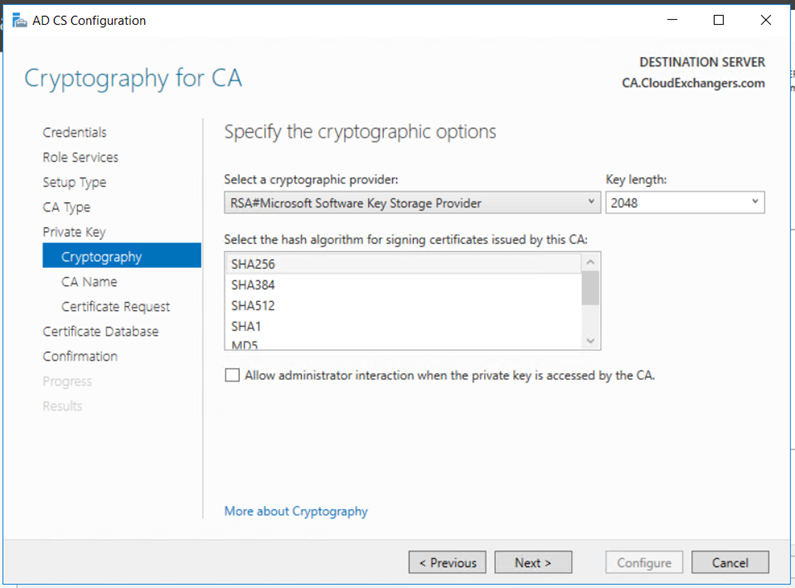
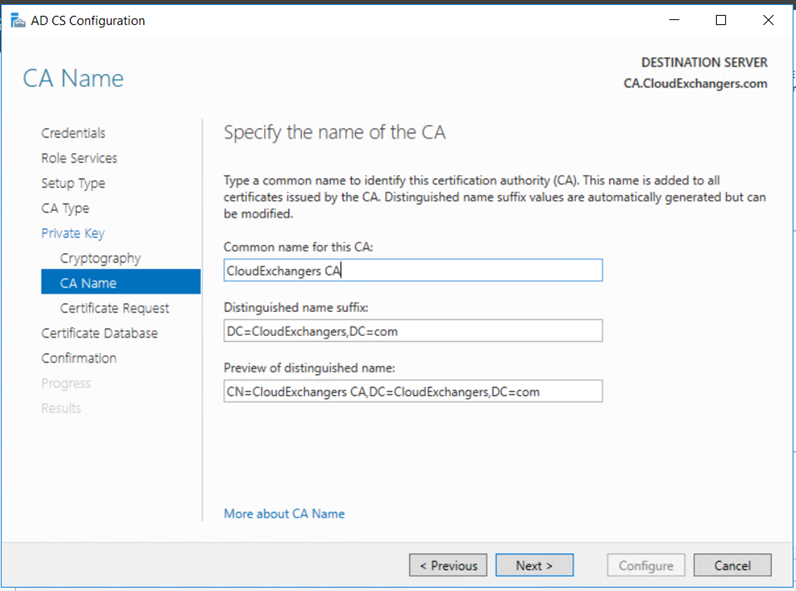
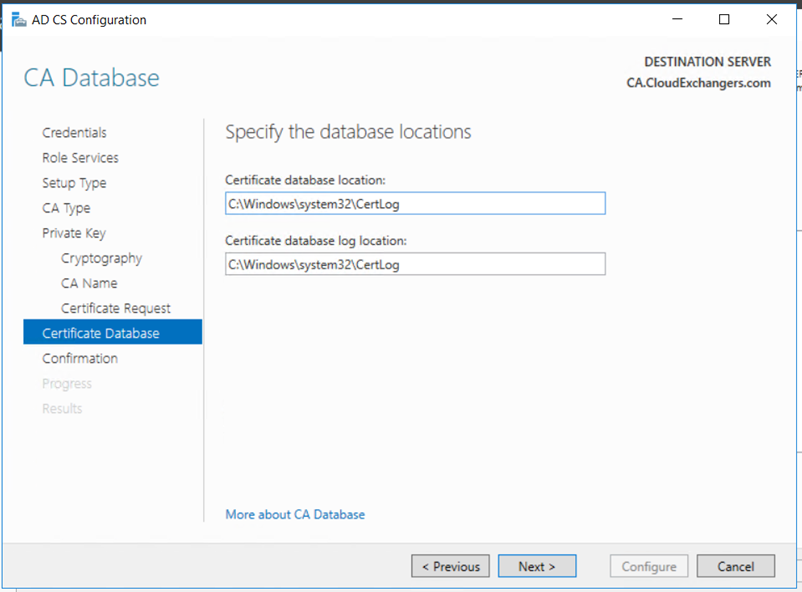
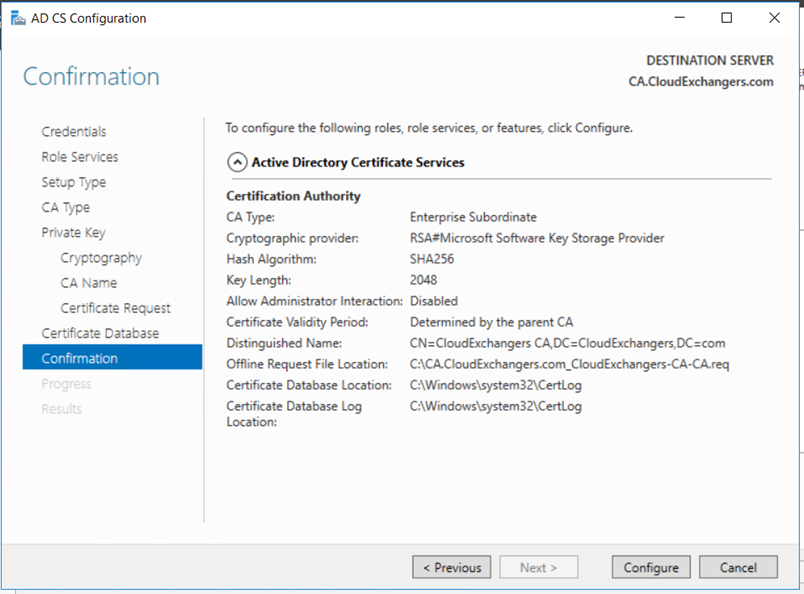
Enterprise Subordinate Issuing CA
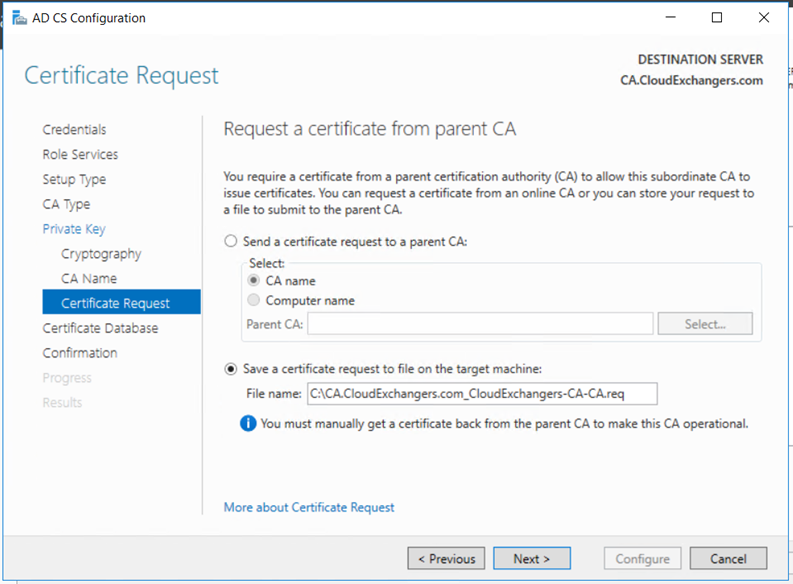
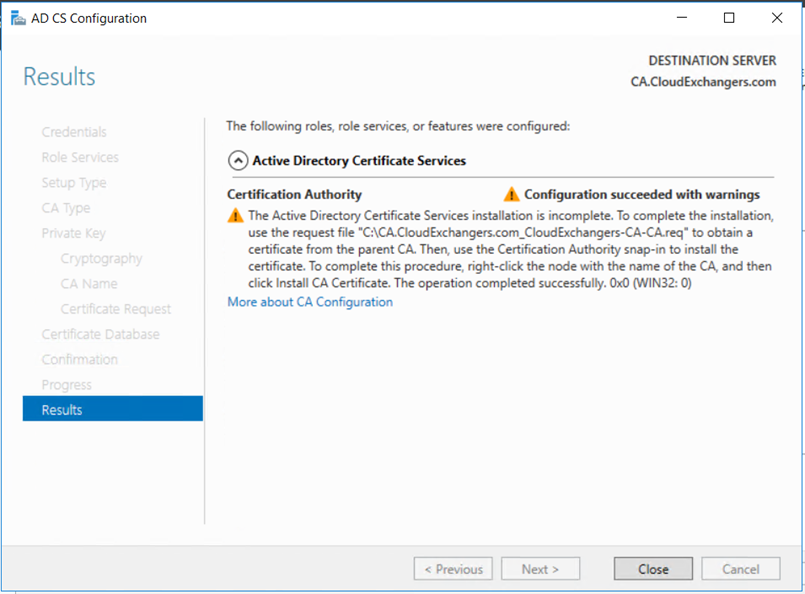
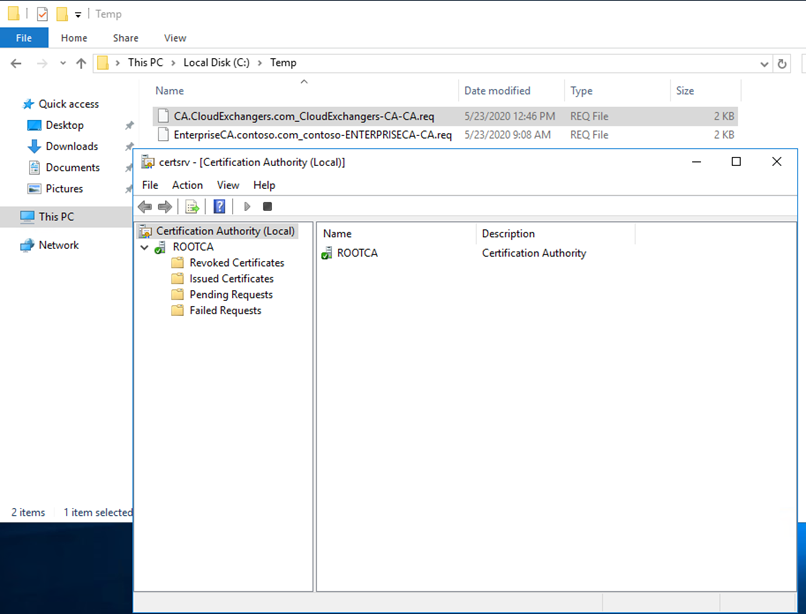
Copy the request file from the Issuing CA to the Root CA and get the certificate for the Cloud Exchangers CA
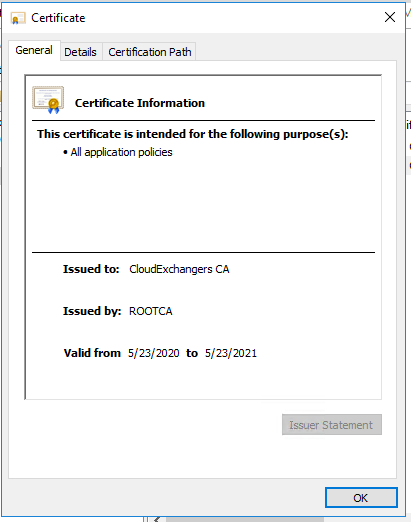
Before we install the certificate, we must publish the Root CA certificate in the CloudExchangers.com active directory so that the Issuing CA will trust the Root CA. This is one of the most important steps and this would avoid any errors while starting the Enterprise Issuing CA.
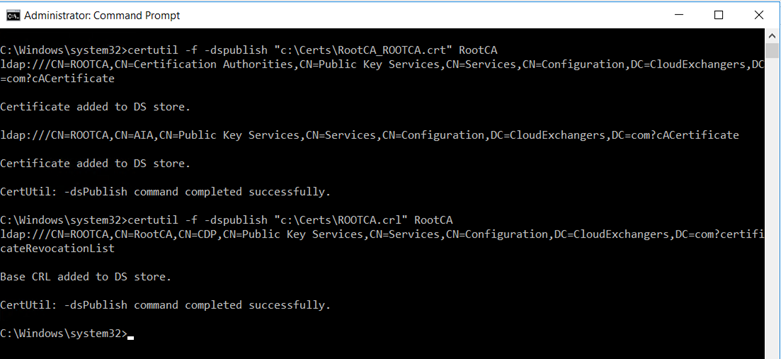
Copy the Root CA certificate and CRL and copy it to the Enterprise CA and run the below commands,
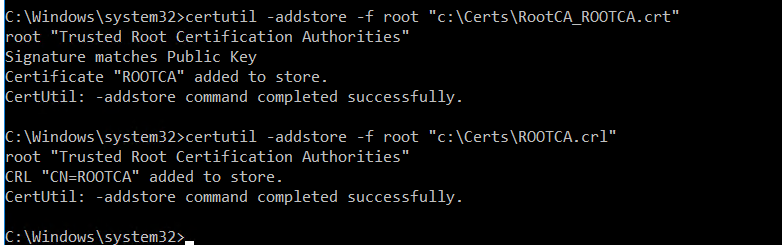
Once it is published it the active directory. Add the certificates to the local store of the Enterprise CA
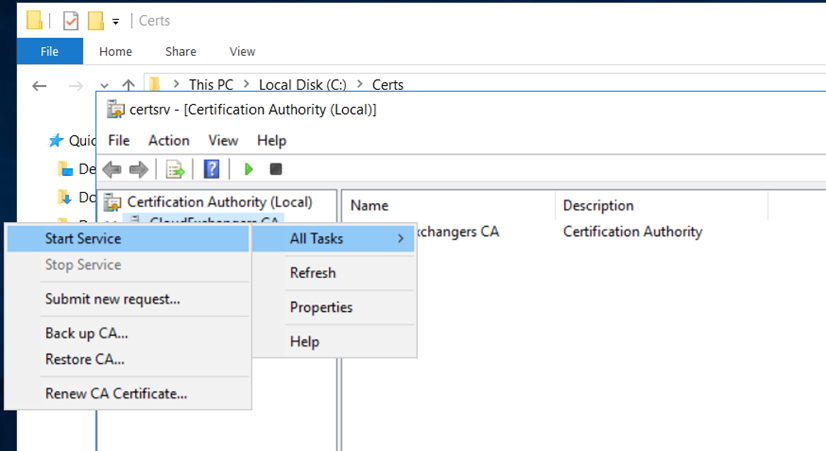
Start the service and it should start without any issues
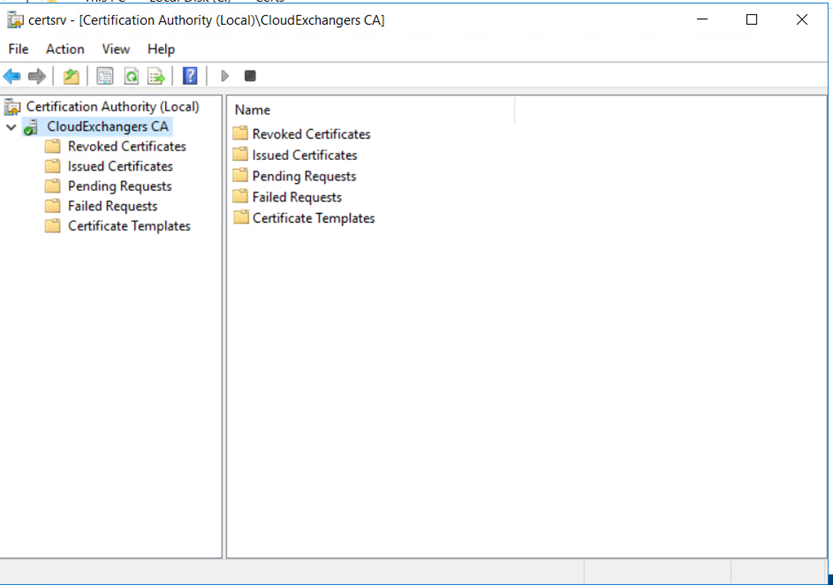
That’s awesome! We have successfully deployed the Enterprise Subordinate CA in cloudexchangers.com by making the use of the same Root CA.
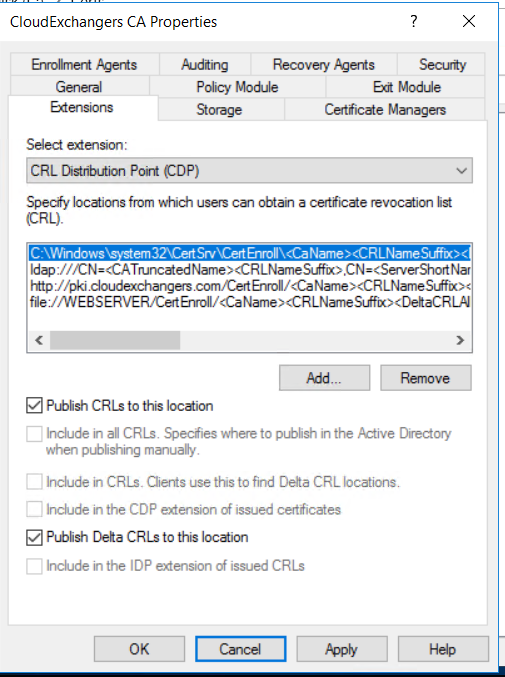
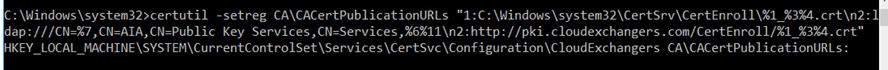
Below is the post configuration for CDP & AIA Extensions,
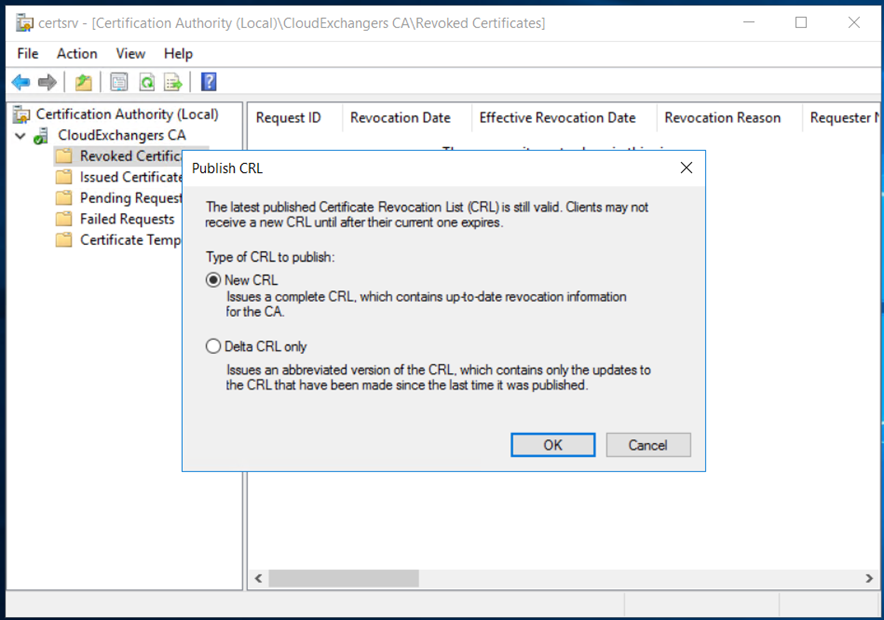
Publish the CRL,
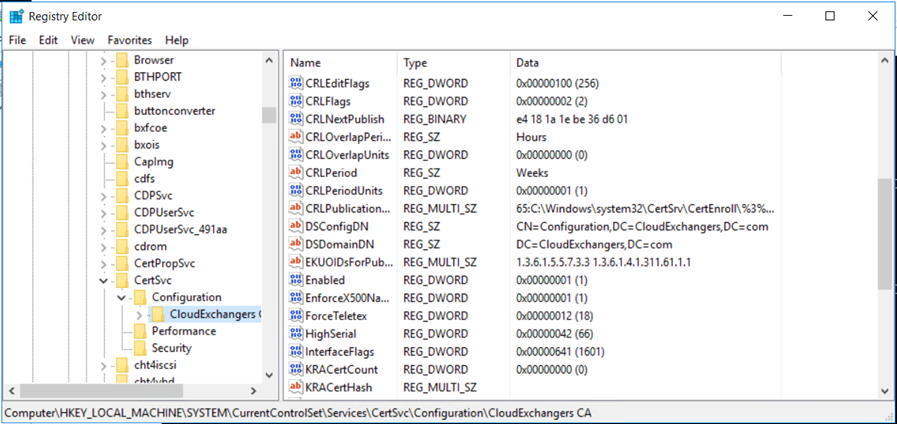
Verify the DSConfigDN in the CloudExchangers.com
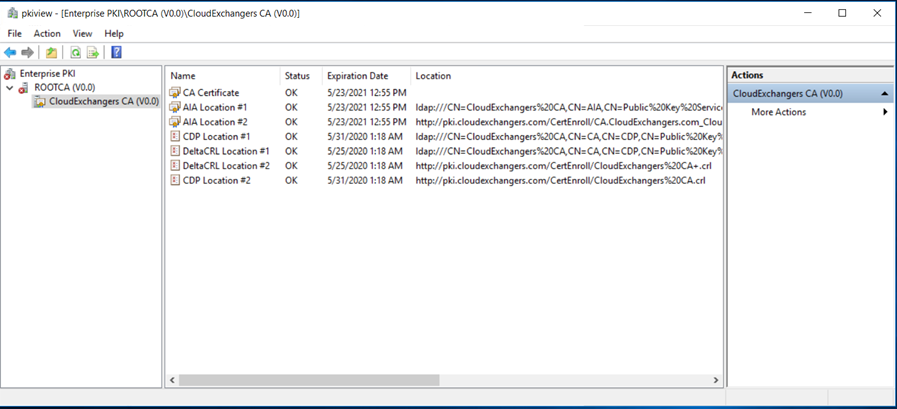
Open the PKIview.msc to check the health of the PKI infrastructure. Root CA’s CRL will not be accessible and it will show as unable to download as expected. If both the forest has network communication, then with the required network routing and firewall rules from the Enterprise Issuing CA in cludexchangers.com to the HTTP location in the contoso.com, this can be rectified.
Finally, with this we have successfully deployed the multi forest active directory certificate services. I hope this article has been useful.
Happy learning!! 🙂
References: