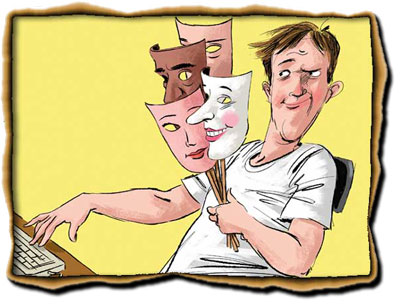
Spoofing is the forgery of an Email address to steal data or to spread malware. Since it appears to originated from one source (mostly looks like the one you trust) when it was sent from different source so often organization users will not realize that the mails are not sent by genuine sender. The intention of spoofing is to make the recipients to take an action or even respond to, their solicitations.
There are 4 types which comes to mind as serious concern:
- Your email address is forged to send emails outside.
- Source is likely to be an individual within the recipient domain.
- Some other critical communication (Example: Bank Communication) address is forged to send mails to your own domain.
- Deliberately sending mails using misspelled domain name.
(We will be discussing all above points in Part2 with possible solution)
Some people get confused with Spoofing and Phishing, basically Spoofing attacks are not necessarily phishing, but phishing is using spoofing strategy. Impersonating someone email address which is most likely known to the target so that the probability of target taking an action on mail increases. Example: If recipient receives email from spoofed bank mail address and it states “We have identified suspicious activity from your account, Immediate password reset is required, please click here to reset password” Of course user clicks on the link which should have some executable content or malware. Phishers always use trustworthy organization email address to get into your network.
Before implementing the solution, we need to first understand that how some spoofs mails are successfully passing through the validation, simple: spammers not just spoofing the “From” address they are also modifying the header information to bypass.
Because there are 2 address types.
- MailFrom address – 5321 address (This is the return path address present in message header) this is often modified to pass SPF tests.
- From address – 5322 address (This is displayed to recipient in “From” field of mail client) this is spoofed address which the user pays attention for.
We will be discussing how to prevent this, however it is always good to educate the user on how to deal with these tricked mails & this is the best way to prevent this at the user level.
Tips to find spoofing/phishing message:
- Mails will have from address as *@YourDomain.com (Example: [email protected])
- If it asking for any information to be replied, just click on “Reply” button to see if the address is getting changed to something else. (Do not hit send) Most of the phishing Emails will have different “ReplyTo” address
- Critical Phishing email body of the message contains “Wire Transfer”
- Any content asking for any personal/ other sensitive information.
- Any link to update your password or to take any action.
All these should be immediately reported to local IT Support or an admin to make sure necessary actions are taken.
How to prevent this as an admin?
There are 3 different methods which can prevent spoofing, I am also going to add one more which can immediately stop this in Hosted Office365 environment.
- SPF (Sender Policy Framework)
- DKIM (Domain Keys Identified Mail)
- DMARC (Domain-based Message Authentication, Reporting & Conformance)
- Transport Rules to reject SPOOFED Emails from yourowndomain.com (Optional)
I will be explaining in detail about above mentioned methods in Part 2.
Feel free to comment for any suggestions.
(to be continued…)