Email encryption is an added layer of security to protect being read by non-intended recipients. Even though office 365 is doing secured transmission using TLS (Transport Layer Security) OME is to build more secured mail transactions. Earlier office 365 version which is FOPE/Wave14 encryption needed separate Microsoft hosted Encryption license and tokens were issued by reputed service provider called “Voltage” but with multiple enhancement current version has got in built encryption technology in Office 365.
Prerequisites:
To enable encryption in Office365 all we need is the active Azure Rights Management License, Bu default it is available in E3 & E4 Subscriptions, for all other subscription you can purchase as an add on for just 2$/user/month.
How to?
Enabling Encryption is not that difficult: We just have to,
- Activate Azure Rights Management License. (If already activated, proceed to next step)
- Configure Azure Rights Management
- Configure Transport Rule based on requirement
Activate Azure Rights Management License
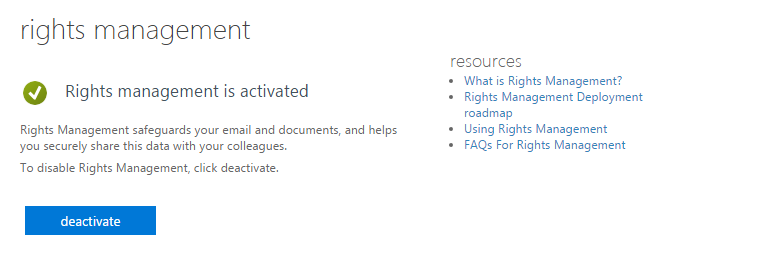
Login to Office365 Portal- Service Settings on Left Pane- > Rights Management-> Manage
- Click on “Activate”
Below is the screen, You will see post activation.
Configure Azure Rights Management:
- First Connect to Exchange Online Powershell
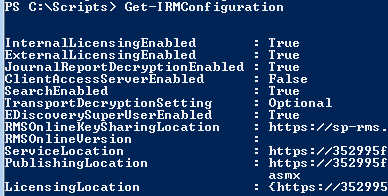
- Run : Get-IRMConfiguration & make sure IRM is not enabled (If already enabled, You saved lot of time, Just transport rule is pending)
Refer table & choose URL of your region.
| Location | RMS key sharing location |
|---|---|
| North America | https://sp-rms.na.aadrm.com/TenantManagement/ServicePartner.svc |
| European Union | https://sp-rms.eu.aadrm.com/TenantManagement/ServicePartner.svc |
| Asia | https://sp-rms.ap.aadrm.com/TenantManagement/ServicePartner.svc |
| South America | https://sp-rms.sa.aadrm.com/TenantManagement/ServicePartner.svc |
| Office 365 for Government (Government Community Cloud) | https://sp-rms.govus.aadrm.com/TenantManagement/ServicePartner.svc1 |
Example : For asia below is IRM configuration
- Set-IRMConfiguration -RMSOnlineKeySharingLocation “https://sp-rms.ap.aadrm.com/TenantManagement/ServicePartner.svc”
- Import-RMSTrustedPublishingDomain -RMSOnline -name “RMS Online”
- Run the following commands to disable IRM templates from being available in OWA and Outlook and then enable IRM for your cloud-based email organization to use IRM for Office 365 Message Encryption:
To disable IRM templates in OWA and Outlook:
Set-IRMConfiguration – ClientAccessServerEnabled $false
To enable IRM for Office 365 Message Encryption:
Set-IRMConfiguration -InternalLicensingEnabled $true
Post configuration you will see it as below:
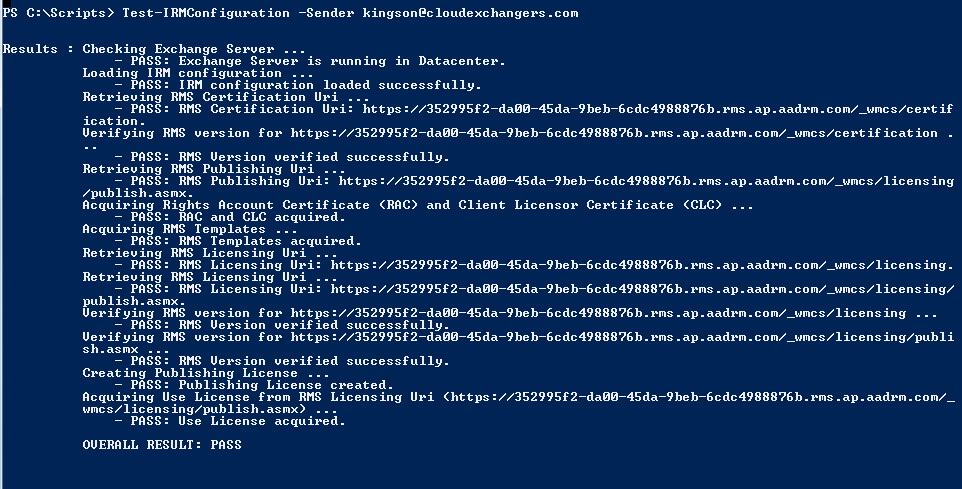
To make sure all configured properly, You can run test by running “Test-IRMConfiguration -Sender [email protected]
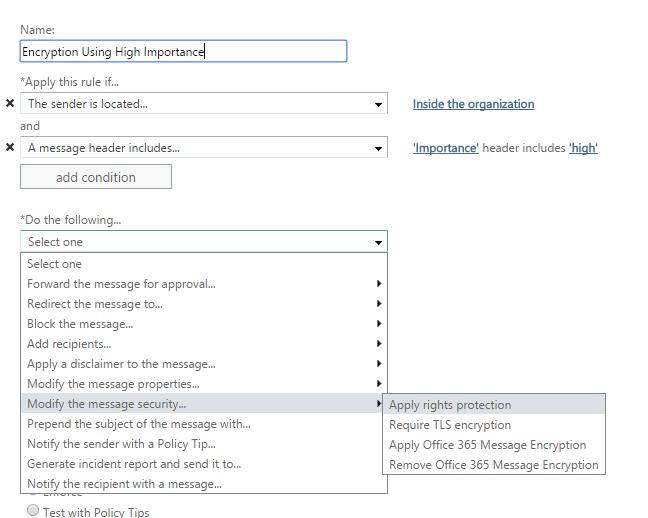
Configure Transport Rule
Microsoft Technet has the detailed information on how to create transport rules with screenshot to apply encryption on messages. Based on your requirement you can customize the conditions to get the message encrypted.
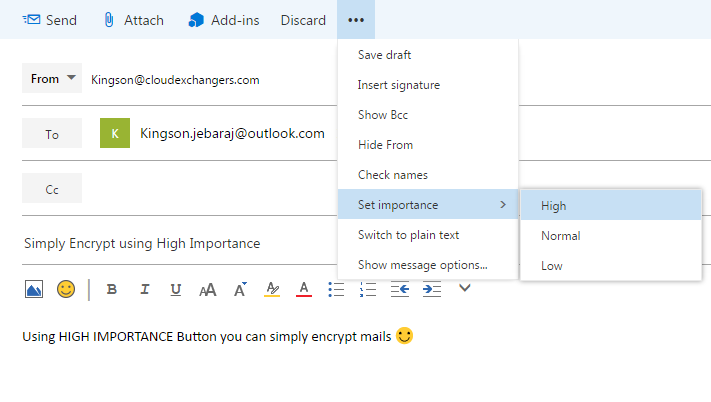
Example, for me the encryption process should be simple so I need all my “High Importance” email should be encrypted, In this case I can simply click on “High Importance” button in Outlook/OWA and mails will be encrypted.
Below is the simple rule to achieve this requirement
After doing this all, I need to do is to simply click on “High Importance” and send the mail.
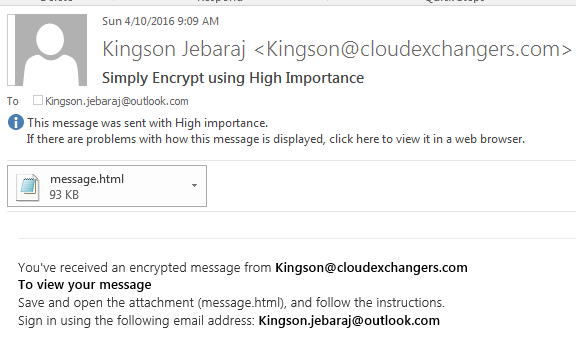
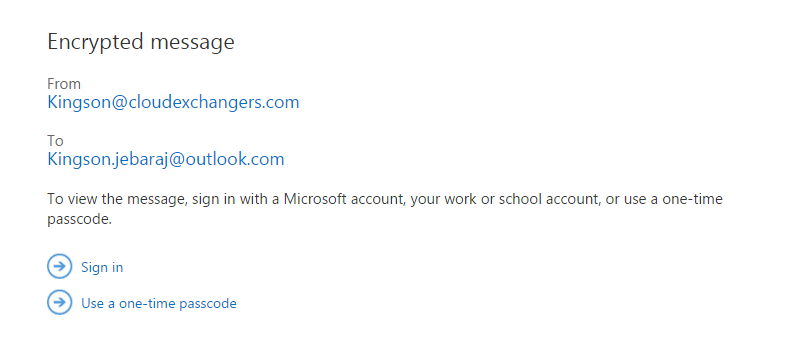
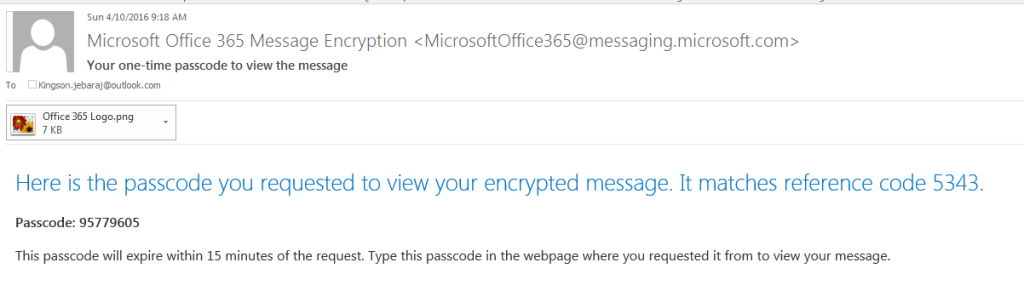
You can simply sign in using you Microsoft account, or use one time passcode to view the mail.
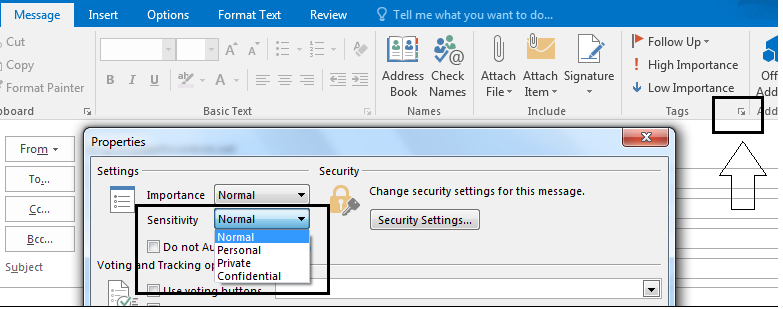
We can also create rule for confidential mails, By mentioning the condition for header Sensitivity: company-confidential.
Doing this we can change the sensitivity in outlook and send mails.
There are lot more you can do with transport rules to make it more effective way of processing mails.
References:
- Office 365 Message Encryption
- Office 365 Message Encryption FAQ’s
- More Details about Encryption
- Define rules to encrypt or decrypt email messages
Feel free to comment below for any suggestions or questions 🙂

content material governance is exceptionally beneficial, thanks for the articles that your self include furnished:)
I have been browsing online more than three hours today, yet I never found any interesting article like yours. It pretty worth enough for me. In my view, if all site owners and bloggers made good content as you did, the web will be much more useful than ever before.
Very nice article. I definitely love this website.
Thanks!
Thank’s great post.
This is very interesting, You’re a very skilled blogger.